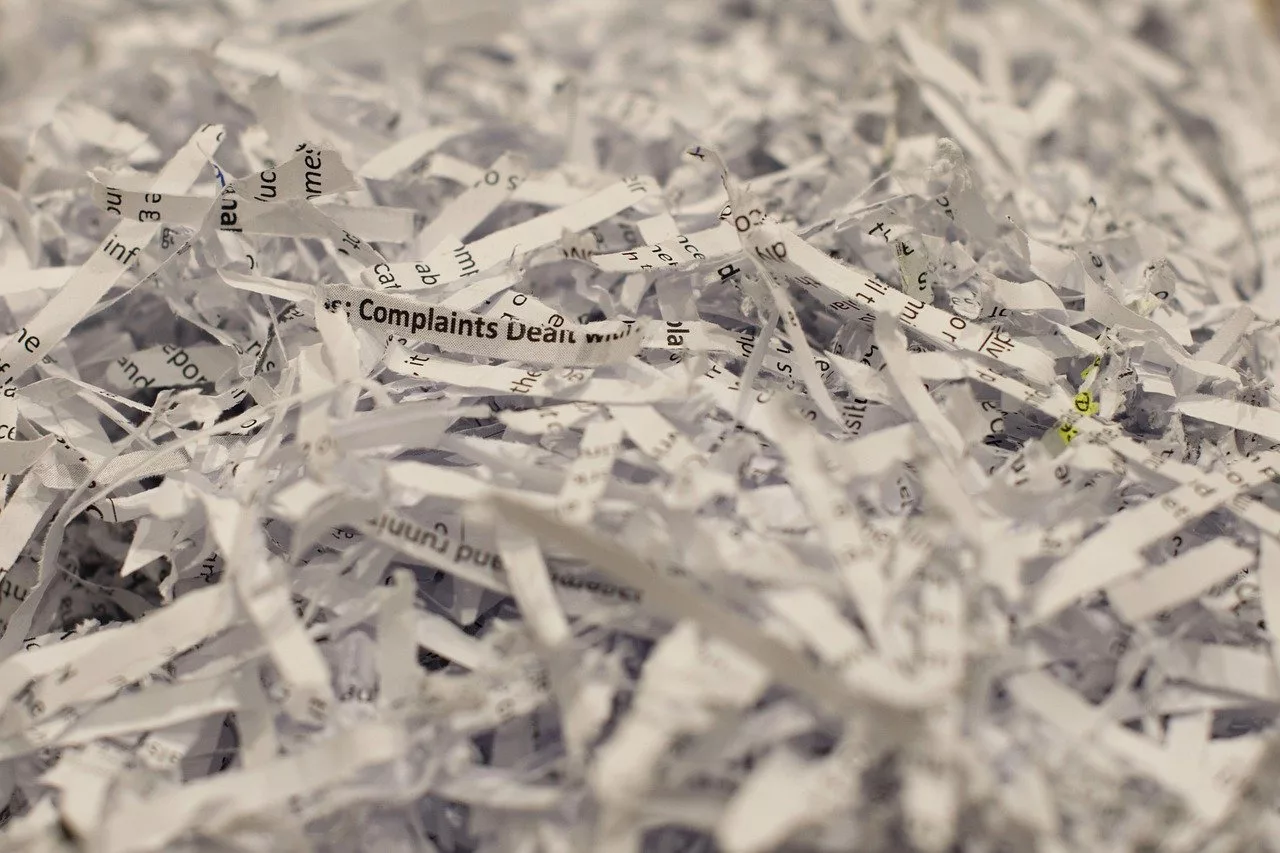
When it comes to the disposal of sensitive information, there are multiple options at your disposal that cater to specific needs. While confidential document shredding services have been around for decades, their popularity has increased in recent years due to stricter data protection regulations and the prevalence of cybercrime. The below article outlines the different shredding methods as well as their security implications.
Importance of Document Destruction
There are a number of reasons why you might want to destroy documents – both old and new. If you are disposing of sensitive data, it is important to consider the above methods of shredding and choose an option that best fits your needs. This will help prevent unwanted individuals from accessing your information and allow you to remain compliant with the Australian Privacy Act 1988:- Companies are increasingly adopting a “dispose as you go” policy, which involves immediate data destruction following its intended use. This allows for a more efficient workflow and prevents information from accidentally falling into the wrong hands. – Individuals that work from home are also encouraged to adopt a similar strategy, as this will help avoid the risk of identity theft or fraud. – Disposing of documents correctly also has implications for businesses that offer or accept payment by check. This can be a tricky area, as any financial documents must be stored for a set period of time to comply with anti-money laundering regulations.
Strip-Cut Shredding
Strip-cut shredding has been around for decades and is one of the more popular methods of shredding. It involves feeding paper into a rotating mechanism that uses sharp cutting blades to slice the paper into strips. Strip shredding is quite affordable and is used to destroy documents that do not require a high level of security. The main benefit of strip-cut shredding is that it is one of the fastest methods of shredding – thereby saving you time and effort. However, it does not offer any form of security as the strips are easily reassembled. It also does not destroy documents well, making it less efficient than other shreds.
Cross-Cut Shredding
Cross-cut shredding is one of the most common methods of shredding and is used in both commercial and domestic settings. It involves the use of rotary blades to cut paper into short pieces that cannot be reassembled. This method is great for destroying confidential papers, credit cards, and other sensitive information. There are different types of cross-cut shredders available. They vary in terms of the number of cutting blades, the size of shredded pieces, and the efficiency of the blades. More sophisticated models will be better at destroying documents, though they will also come with a higher price tag.
Particle-Cut Shredding
Particle-cut shredding is a method used for industrial-grade shredding. It shreds documents into tiny, unreadable particles that cannot be reassembled. This method is often used for destroying sensitive information, such as client details and medical records. The main benefit of particle-cut shredding is that it is difficult for anyone to reassemble the pieces and extract information from them. However, this method is expensive and is only suitable for large-scale operations.
Pierce & Tear Shredding
Pierce-and-tear shredders are used to destroy sensitive documents and are a popular option in both commercial and domestic settings. They work by piercing documents with a rotating blade, followed by ripping them into pieces. The rotating blades can be adjusted according to the desired level of security. The main benefit of a pierce-and-tear shredder is that it offers a high level of security, as it destroys documents at the molecular level. A potential drawback of this method is that it often requires higher maintenance compared to other shredding options.
Conclusion
When it comes to the disposal of sensitive information, there are multiple options at your disposal that cater to specific needs. While confidential document shredding services have been around for decades, their popularity has increased in recent years due to stricter data protection regulations and the prevalence of cybercrime. The above article outlines the different shredding methods as well as their security implications.When choosing a shredding method, it is important to consider the level of security you need, the amount of time and effort you are willing to spend, and the cost of shredding.